Strict Transport Security and Preloading
You've probably heard that HTTPS makes websites more secure. That's true, but HTTPS has some limitations, and Strict Transport Security and Preloading are ways you can overcome those limitations.
1. what does HTTPS do?
HTTPS adds encryption to the connection between two computers and a server you're connecting to. That means
that anyone with the ability to listen in on your connection can't actually see any of the stuff you're
transmitting. They can see which website you're connecting to. For example, if you're googling
something, they can see that you're connected to www.google.com , but they can't see the term you
searched for.
HTTPS also ensures that the server you're connecting to is the correct server for the domain you're visiting. Without it, an attacker could send you to a fake version of any website. To make that verification work, every HTTP server must present a public certificate for its domain, and browsers make sure that certificate is valid. To get a valid certificate, you need approval from a certificate authority, and those authorities generally make sure that you actually own the domain before giving you a certificate.
2. why do you need HTTPS?
Multiple bad things could happen if you connect to a website with plain HTTP, without encryption. First, your internet provider could monitor everything you do on that website. They could see which subpages you visit and if you enter anything into a form (like your name or password or a credit card number), they could see that too. They could also change what you see in your browser (for example by injecting ads that aren't part of the website itself).
Your internet provider would probably collect and store that data (in many countries they would actually be required to). They would also be forced to hand it over to the government when it asks for it.
Anyone else who manages to get access to your connection could also do all those things and even worse. If you download a piece of software via an insecure connection, an attacker could inject their own malware into that download.
HTTPS has some other advantages too: secure websites are faster, better for the environment and favored by search engines.
3. the first connection is insecure
When you type an address like www.google.com in your browser address bar, it will likely first
attempt to connect via HTTP. The google server will return a response that redirects to HTTPS. However, that
first interaction is unencrypted, meaning that an attacker could intercept the response and change it so it
redirects to an entirely different page. For example, a phishing page that looks like google, but when
you enter your login credentials there, they are sent to the attackers computer.
4. Strict-Transport-Security: making the first connection secure
Web servers can send an additional header called Strict-Transport-Security as part of their
response. This header tells browsers that they should always connect to this domain via HTTPS, which
would prevent the above attack. In its simplest form the header has only a single property:
Strict-Transport-Security: max-age=63115200max-age is the policy lifetime in seconds (here: two years).
You can also add the includeSubDomains directive, which tells the browser that the policy applies to
all subdomains below the current domain.
5. the first first connection is still insecure
You may have already noticed this: Strict-Transport-Security is a response header, meaning that it's
only sent once you connect to a server. That means that the very first connection your browser ever makes to a
website might still be over an insecure connection and could be vulnerable to attack.
6. HSTS preloading: making every connection secure
There is a file in every modern browser called the preload list. If a domain is on that list, the browser will
always connect to it via HTTPS, even on the very first connection, and even if you explicitly type http://
in your address bar. This is in fact the only way to be reasonably sure that nobody can intercept a connection
to that website.
If you want to get your website on the preload list, there are a few steps:
- Make sure that your site and all subdomains work with HTTPS, and that all users you care about can use HTTPS (that's probably the case, but just be sure).
- Serve a header like
Strict-Transport-Security: max-age=63115200; includeSubDomains; preload. Themax-agemust be at least one year, but two years are recommended.includeSubDomainsis mandatory, you can only preload an entire eTLD + 1. - Go to https://hstspreload.org and enter your domain.
- If the page is green, you should see a form allowing you to submit your page to the preload list. Confirm the questions and submit the form.
- Wait - until the next release of each browser.
You can then re-check on https://hstspreload.org and it should say that your domain is on the preload list. Congrats, from now on every connection will be secure!
7. another problem: certificate warnings
There is another problem with HTTPS: I said at the beginning that HTTPS prevents domain impersonation, because you need a valid certificate. Well, what happens if you simply present an invalid certificate? The browser will show a warning like this:
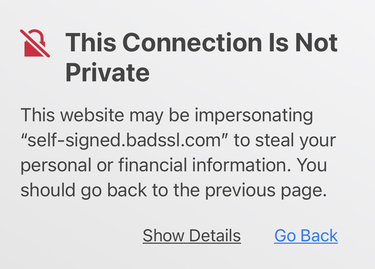
The warning shown in Safari makes it pretty sure that there's a security risk. That's already a big improvement over what these warnings used to look like:
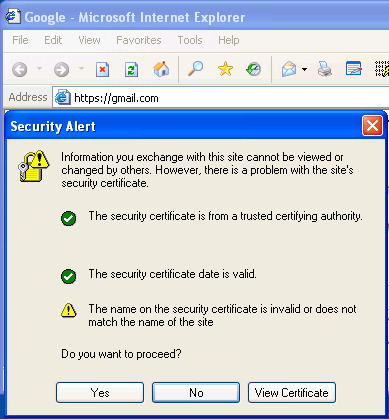
However, when you click on "Show Details", Safari still has an option to circumvent the warning:
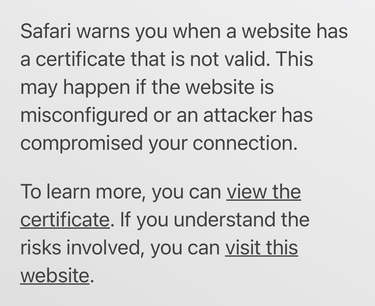
A skilled social engineer could probably get many internet users to click that button and connect to a dangerous site.
Here's the good news: HSTS preloading solves that problem! When you connect to a site on the preload list, and the server returns an invalid certificate, the warning looks like this:
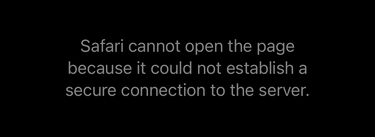
There is no way to circumvent the warning! This is the case in Firefox, Chrome, and Safari.
8. conclusion: use HSTS preloading!
HSTS preloading is the best way to keep your visitors reasonably safe from a long list of potential attacks. It's free if you get your HTTPS certificate from Let's Encrypt, which I highly recommend.